Command and Control (C2) Servers: The Backbone of Modern Cyber Attacks
Command and Control (C2) servers play a critical role in modern cyber attacks by allowing hackers to control infected systems remotely. This guide explains how C2 servers work, their key features, and how to defend against them.
Cyber attacks today are no longer simple, one-time events. They are structured, controlled, and often operate like a coordinated system. At the center of many advanced attacks is something called a Command and Control (C2) server.
Think of a C2 server as the “remote control” that hackers use to manage infected devices. Once a system is compromised, it doesn’t act alone—it communicates with a central server that tells it what to do next.
Understanding how C2 servers work is essential to detecting and preventing modern cyber threats.
🧠 What is a Command and Control (C2) Server?
A Command and Control server is a system used by attackers to send instructions to infected devices (also called bots).
Once malware infects a device, it connects back to the C2 server and waits for commands.
👉 These commands can include:
- Stealing data
- Spreading malware
- Launching attacks on other systems
- Monitoring user activity
How C2 Servers Work (Simple Breakdown)
1. Initial Infection
The attacker infects a system using phishing, malicious downloads, or vulnerabilities.
2. Connection to C2 Server
The infected system secretly connects to the attacker’s server.
3. Command Execution
The server sends instructions, and the infected system follows them.
4. Continuous Communication
The system keeps communicating with the C2 server to receive updates.
👉 This creates a controlled network of infected devices.
What is a Botnet?
When multiple infected systems connect to a C2 server, they form a botnet.
👉 A botnet can be used for:
- DDoS attacks
- Mass data theft
- Spam campaigns
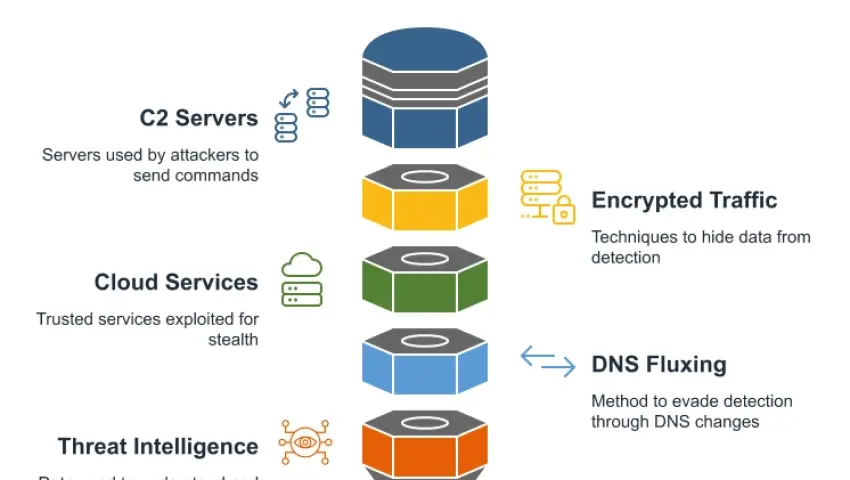
Key Features of C2-Based Cyber Attacks
✔️ Remote Control Capability
Attackers can control systems from anywhere in the world
✔️ Stealth Communication
Communication is hidden to avoid detection
✔️ Scalable Attacks
Thousands of infected systems can be controlled at once
✔️ Persistent Access
Even after reboot, malware reconnects to the C2 server
✔️ Encrypted Traffic
Data between infected systems and C2 servers is often encrypted
How C2 Traffic Stays Hidden
Attackers use advanced techniques to avoid detection:
- Using normal-looking internet traffic
- Frequently changing server locations
- Using legitimate services to hide communication
- Encrypting data to prevent inspection
👉 This makes C2 attacks difficult to detect with basic security tools.
Signs Your System Might Be Connected to a C2 Server
- Unusual outgoing network traffic
- Slow system performance
- Unknown background processes
- Connections to suspicious domains
👉 These signs should never be ignored.
How to Detect and Prevent C2 Attacks
Monitor Network Traffic
Track unusual communication patterns and unknown connections
Use Advanced Security Tools
Use Endpoint Detection and Response (EDR) and intrusion detection systems
Keep Systems Updated
Fix vulnerabilities that attackers use to gain access
Avoid Phishing Attacks
Do not click on unknown links or download suspicious files
Network Segmentation
Limit how far an attacker can move within a network
Real-World Insight
Many major cyber attacks rely on C2 infrastructure. Without it, attackers would lose control over infected systems.
In several cases, once the C2 server is identified and shut down, the entire attack operation collapses.
👉 This shows how critical C2 servers are in modern cyber attacks.
SEO Keywords
- command and control server
- C2 server cybersecurity
- botnet attacks explained
- how hackers control systems
- advanced cyber attack techniques
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

