Cyber Forensic Tools & Techniques: How Digital Investigations Really Work
Whenever a cybercrime happens — like hacking, fraud, or data theft — someone has to investigate it. That’s where cyber forensics comes in. Cyber forensics is the process of collecting, analyzing, and preserving digital evidence so that criminals can be identified and caught. In 2026, it has become a powerful field used by police, investigators, and cybersecurity experts.
What is Cyber Forensics?
Cyber forensics (or digital forensics) is all about:
- Finding digital evidence
- Recovering deleted data
- Tracking cybercriminal activity
👉 It works just like traditional investigation — but in the digital world.
Why Cyber Forensics is Important
- Helps solve cybercrime cases
- Recovers lost or deleted data
- Provides legal evidence in court
- Tracks hackers and fraudsters
Top Cyber Forensic Tools (2026)
1. Autopsy
A popular open-source tool used to:
- Analyze hard drives
- Recover deleted files
- Investigate system activity
2. FTK (Forensic Toolkit)
Used by professionals for:
- Data analysis
- Password recovery
- Email investigation
3. EnCase
One of the most advanced tools used by:
- Law enforcement agencies
- Corporate investigators
4. Cellebrite
Used for mobile forensics:
- Recover deleted WhatsApp chats
- Extract phone data
- Analyze call logs
👉 Keyword: mobile forensic tools
5. Wireshark
Used to analyze network traffic:
- Detect suspicious activity
- Track data transfer
6. Magnet AXIOM
Helps in:
- Recovering files
- Analyzing user behavior
- Case management
Key Cyber Forensic Techniques
1. Data Recovery
Even deleted files can be recovered using forensic tools.
👉 Important:
Deleting a file doesn’t mean it’s gone permanently.
2. Disk Imaging
Creating an exact copy of a storage device.
👉 Why?
- Original data remains untouched
- Used as legal evidence
3. Log Analysis
Investigators analyze logs to track:
- Login attempts
- User activity
- Suspicious behavior
4. Email Analysis
Used to:
- Track sender
- Identify phishing attacks
- Recover deleted emails
5. Network Forensics
Monitoring and analyzing network traffic to detect:
- Attacks
- Data leaks
- Unauthorized access
6. Mobile Forensics
Focused on smartphones:
- Recover chats
- Extract media files
- Analyze app usage
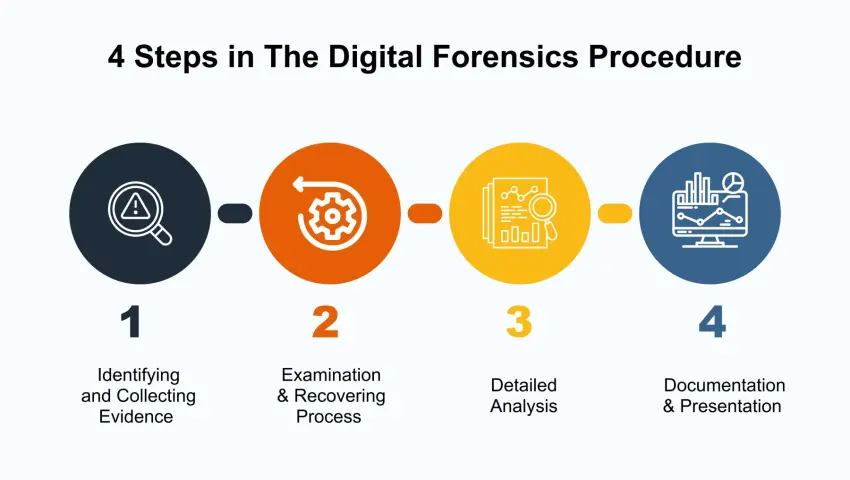
How Cyber Investigation Works (Step-by-Step)
- Identification – Detect the incident
- Collection – Gather digital evidence
- Preservation – Keep data safe (no changes)
- Analysis – Examine data
- Reporting – Present findings
Legal Importance
Cyber forensic evidence is used in:
- Court cases
- Cybercrime investigations
- Corporate fraud cases
👉 Proper handling is important, otherwise evidence may be rejected.
Real-Life Example
A fraud case where money was transferred illegally.
👉 Investigators used:
- Mobile forensics to check chats
- Log analysis to track login
- IP tracking to identify location
👉 Result: Criminal was caught
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

