How Intelligence Agencies Track Criminals Using Digital Footprints (CDR, IPDR Explained)
In today’s digital world, almost everything we do leaves a trace — whether it’s making a phone call, browsing the internet, or using social media. These traces are known as digital footprints, and they play a crucial role in modern investigations.
Intelligence agencies like the CBI , CIA , and Mossad rely heavily on these digital footprints to track criminals, uncover networks, and solve complex cases.
In this article, we’ll break down how digital tracking works and explain key concepts like CDR (Call Detail Record) and IPDR (Internet Protocol Detail Record) in simple terms.
📡 What Is a Digital Footprint?
A digital footprint is the trail of data you leave behind when you use digital devices or the internet.
Every action creates a record, such as:
- making a phone call
- sending a message
- visiting a website
- logging into an app
Even if you think you’re being careful, these traces are often stored by telecom companies and internet service providers.
👉 In investigations, this data becomes valuable evidence.
📞 What Is CDR (Call Detail Record)?

CDR stands for Call Detail Record. It is a log maintained by telecom operators that records details of phone calls and SMS activity.
A typical CDR includes:
- phone numbers involved in the call
- call duration
- date and time
- cell tower location
👉 This means investigators can see who called whom, when, and from where (approximate location).
For example, if a suspect communicates frequently with unknown numbers, CDR analysis can help uncover hidden connections.
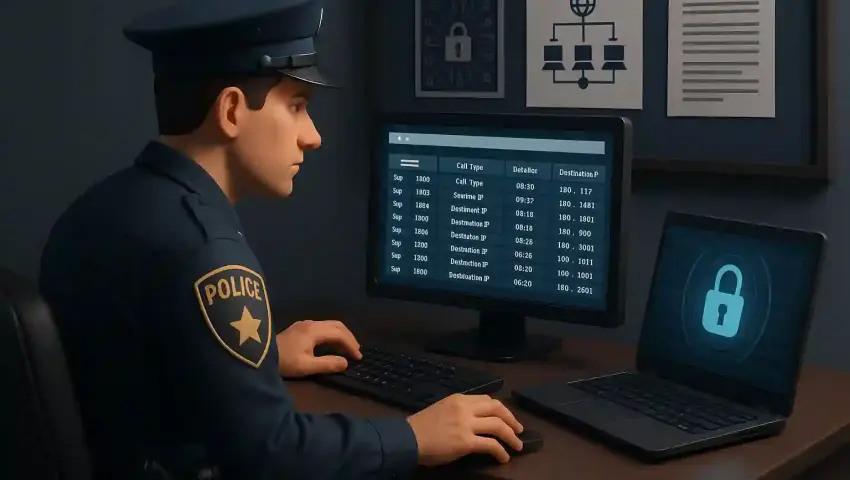
🌐 What Is IPDR (Internet Protocol Detail Record)?

IPDR stands for Internet Protocol Detail Record. It tracks internet activity instead of phone calls.
An IPDR may contain:
- IP address used
- websites visited
- login timestamps
- device information
👉 This helps agencies understand online behavior and activity patterns.
For instance, if someone accesses suspicious websites or uses anonymous services, IPDR data can reveal those actions.
📍 How Agencies Track Location
Tracking a person’s location doesn’t always require GPS. Agencies can use telecom data to estimate location.
📡 Cell Tower Triangulation
When a phone is active, it connects to nearby towers. By analyzing signals from multiple towers, investigators can estimate a person’s location.
🌍 IP-Based Location Tracking
IP addresses can provide:
- approximate city or region
- internet service provider details
👉 While not 100% accurate, it still gives strong clues during investigations.
🔍 How CDR & IPDR Work Together
Individually, CDR and IPDR are powerful. But when combined, they become even more effective.
Example:
- CDR shows communication between two suspects
- IPDR shows their online activity at the same time
👉 This helps build a complete timeline of events.
Agencies can then connect:
- calls
- messages
- internet usage
to understand the full picture of a crime.
🧠 Real-Life Scenario (Simple Example)
Let’s say a cyber fraud case is reported.
Investigators may:
- Analyze CDR to identify frequent contacts
- Use IPDR to check suspicious online activity
- Track location using tower data
- Connect multiple suspects through shared communication
👉 Step by step, a digital trail is formed — leading to the criminal.
⚠️ Important Note
Digital tracking is not random or unauthorized.
- Agencies require legal permission to access CDR/IPDR
- Data is collected through telecom operators and ISPs
- Privacy laws and regulations must be followed
👉 Misuse of such data is strictly illegal.
🏁 Conclusion
In modern investigations, digital footprints have become one of the most powerful tools. From phone calls to internet activity, every action leaves a trace that can be analyzed.
With the help of CDR and IPDR, agencies like CBI, CIA, and Mossad can:
- track suspects
- uncover hidden networks
- solve complex cyber crimes
And the key takeaway is simple —
👉 In the digital world, it’s very hard to leave no trace.
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *





