How to Detect and Prevent Cyber Attacks Before They Happen
Cyber attacks don’t usually happen suddenly—they often leave warning signs. The problem is, most people and even organizations fail to notice them until it’s too late. In 2026, cyber threats are more advanced, automated, and targeted than ever before. Waiting for an attack to happen is no longer an option. The focus has shifted from reaction to prevention.
Cyber attacks rarely begin with obvious damage. In most cases, they start silently—through a phishing email, a weak password, or a small system vulnerability. Attackers don’t rush; they observe, access, and expand their control step by step.
By the time an organization realizes something is wrong, sensitive data may already be compromised. That’s why modern cybersecurity is no longer about reacting to incidents—it’s about detecting threats early and stopping them before they escalate.
Understanding how attacks behave in their early stages gives you a major advantage. Prevention begins with visibility, awareness, and a proactive mindset.
Understanding the Lifecycle of a Cyber Attack
To detect attacks early, you need to understand how they unfold. Most cyber attacks follow a structured path:
1. Initial Access
Attackers gain entry through phishing emails, weak credentials, or unpatched vulnerabilities.
2. Establishing Foothold
Malware is installed or unauthorized access is maintained quietly.
3. Privilege Escalation
Attackers try to gain higher access levels to control more systems.
4. Lateral Movement
They move across networks to find valuable data or systems.
5. Data Exfiltration or Damage
Finally, data is stolen, encrypted, or systems are disrupted.
👉 Key Insight:
The earlier you detect an attack in this chain, the easier it is to stop.
Early Warning Signs You Should Never Ignore
Cyber attacks almost always leave subtle traces. Recognizing these signs is critical.
Unusual System Behavior
- Sudden slowdown without reason
- Unknown processes running
- Frequent crashes or restarts
👉 These may indicate hidden malware activity.
Abnormal Network Activity
- Unexpected spikes in data usage
- Communication with unknown IP addresses
- Data transfers at odd hours
👉 Often a sign of data exfiltration.
Suspicious Login Attempts
- Multiple failed logins
- Access from unfamiliar locations
- Logins at unusual times
👉 Indicates brute-force or credential compromise attempts.
Phishing Indicators
- Emails creating urgency or fear
- Suspicious links or attachments
- Fake login pages
👉 Still one of the most successful attack vectors.
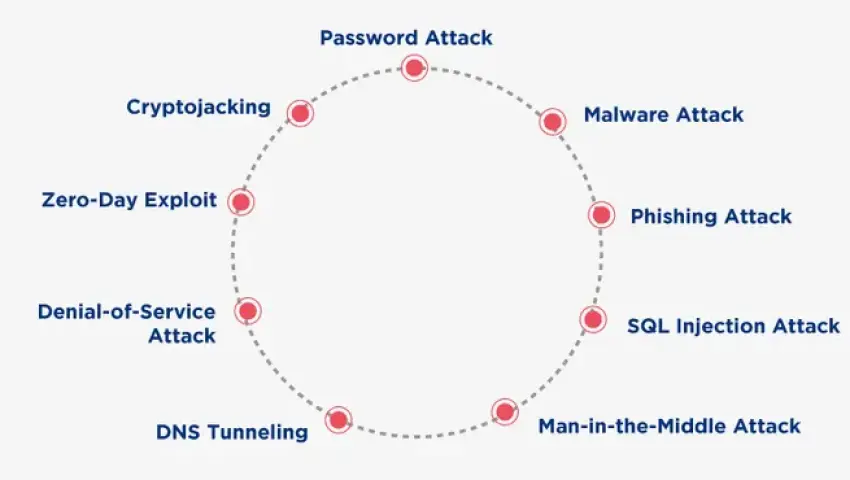
Key Features of Modern Cyber Attacks
✔️ Stealth-Oriented Execution
Attackers design operations to stay hidden for as long as possible, avoiding detection tools.
✔️ Automation and Speed
Bots and scripts allow attackers to scan and attack thousands of systems simultaneously.
✔️ Multi-Stage Attack Chains
Modern attacks combine multiple techniques—phishing, malware, and exploitation—to increase success rates.
✔️ Targeted Attacks
Instead of random attacks, hackers now focus on specific individuals or organizations using collected data.
✔️ AI-Driven Adaptation
Attack methods evolve based on system defenses, making them more effective over time.
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

