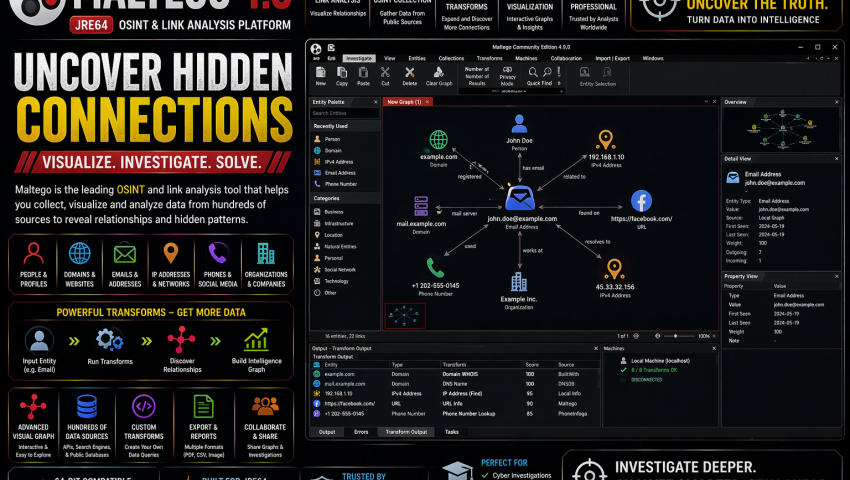
Maltego 4.9 (JRE64) – OSINT & Link Analysis Platform
In modern cyber investigations, collecting information is only half the work—understanding relationships between people, domains, infrastructure, and data points is where real intelligence emerges. Maltego is a powerful OSINT and link analysis platform widely used in threat intelligence, digital investigations, and cybercrime analysis.
Maltego 4.9 (JRE64) is popular among ethical hackers, investigators, SOC analysts, and OSINT researchers for visualizing complex relationships and automating intelligence gathering.
What is Maltego 4.9?
Maltego is an open-source intelligence and graph analysis platform used to discover, map, and visualize connections between entities such as:
- Domains
- IP addresses
- Email addresses
- Social profiles
- Organizations
- Infrastructure indicators
- Threat intelligence artifacts
It helps investigators turn scattered data into connected intelligence.
Key Features
1. Link Analysis Visualization
Maltego is known for visual graph analysis that reveals hidden relationships.
Map connections between:
- People
- Domains
- Infrastructure
- Threat indicators
- Digital identities
2. OSINT Data Gathering
Collect public-source intelligence through automated data collection methods.
Useful for:
- Reconnaissance
- Attribution research
- Threat actor profiling
- Exposure discovery
3. Transforms Automation
One of Maltego’s strongest features is Transforms, which automate data enrichment and pivoting.
Use transforms to:
- Expand investigations
- Correlate indicators
- Discover related infrastructure
4. Threat Intelligence Analysis
Support cyber threat investigations through indicator correlation.
Useful in:
- IOC analysis
- Infrastructure tracking
- Threat actor research
5. Social Media & Identity Analysis
Useful in OSINT profiling and digital footprint mapping.
6. Investigation Graphing
Turn raw intelligence into visual investigation graphs for analysis and reporting.
Use Cases
Threat Intelligence
Map relationships among domains, IPs, and malicious infrastructure.
OSINT Investigations
Gather and correlate public intelligence from multiple sources.
Cybercrime Investigations
Useful for:
- Fraud analysis
- Scam investigations
- Threat actor profiling
- Infrastructure mapping
Ethical Hacking Recon
Support authorized reconnaissance and attack surface discovery.
Digital Investigations
Use graph analysis to uncover patterns hidden in data.
Cybersecurity Focus
From a cybersecurity perspective, Maltego supports:
Threat Hunting
Pivot through related indicators during hunts.
Infrastructure Analysis
Investigate suspicious domains, hosts, and networks.
Reconnaissance
Support authorized information gathering.
Threat Actor Profiling
Map aliases, infrastructure, and relationships.
Common Features Analysts Look For
✔ Graph-based link analysis
✔ OSINT transforms
✔ Threat intelligence enrichment
✔ Entity correlation
✔ Infrastructure mapping
✔ Social footprint analysis
✔ Investigation visualization
✔ Automation support
How It Works
Typical workflow:
- Add starting entity (domain, IP, email, etc.)
- Run transforms
- Discover linked entities
- Build relationship graph
- Analyze connections and intelligence
Where to Download
Download from official or trusted sources only.
Avoid unofficial modified packages.
📥 Where to Buy / Download
To get Maltego 4.9 (JRE64) safely, use your official purchase or download link below:
👉 Buy / Download Maltego 4.9 Here
Recommended for:
- OSINT Analysts
- Threat Intelligence Teams
- Ethical Hackers
- Digital Investigators
- Cybersecurity Students
Pros
- Powerful link analysis platform
- Excellent OSINT investigation support
- Strong visualization capabilities
- Flexible transforms ecosystem
- Widely used in cyber investigations
Limitations
- Advanced workflows may have learning curve
- Some transforms may rely on external data sources or licensing
- Best results often come when combined with other investigation tools
Related Tools Often Used With It
Often paired with:
- SpiderFoot
- theHarvester
- Nmap
Final Verdict
Maltego is a powerful platform for OSINT investigations, threat intelligence, link analysis, and cyber reconnaissance.
Best suited for:
- Threat Intelligence Analysts
- OSINT Researchers
- Ethical Hackers
- Incident Responders
- Cybersecurity Learners
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

