Social Engineering Attacks: How Hackers Manipulate Human Psychology to Breach Security
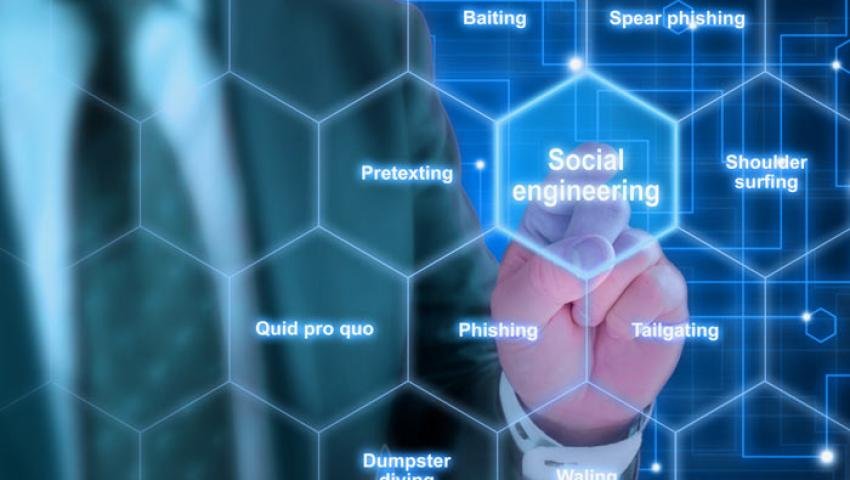
Social engineering attacks exploit human psychology rather than technical vulnerabilities. This in-depth guide explains how these attacks work, their key features, common techniques, and how to prevent them effectively.
Cybersecurity is often seen as a technical problem—but the reality is very different. Today, the biggest vulnerability is not software or systems, but humans themselves.
Hackers have realized that breaking through firewalls is difficult, but manipulating people is much easier. That’s why social engineering attacks are becoming increasingly powerful and dangerous.
These attacks work quietly—no alerts, no warnings. Just one wrong decision, and an entire system can be compromised.
👉 The real battlefield of cybersecurity has now shifted to human psychology.
How Hackers Think (Attacker Mindset)
To truly understand social engineering, it’s important to understand how attackers think.
Hackers don’t just study systems—they study people:
- Who trusts easily
- Who reacts under pressure
- Who makes mistakes in urgency
👉 Their goal is simple:
“Convince the user so well that they willingly give access themselves.”
How Social Engineering Attacks Actually Work (Real Flow)
1. Target Research
The attacker first gathers information about the victim
(social media, LinkedIn, company websites)
2. Trust Building
They impersonate a trusted entity
(IT support, bank, colleague)
3. Psychological Trigger
The victim is pushed to act quickly using emotions like:
- Urgency (“Your account will be blocked”)
- Fear (“Suspicious activity detected”)
- Curiosity (“You received a payment”)
4. Exploitation
The victim unknowingly shares sensitive information or performs a risky action.
👉 The attack succeeds without using any advanced hacking tools.
Key Features of Social Engineering Attacks
✔️ Psychology-Based Exploitation
Targets human emotions like fear, trust, and urgency
✔️ Zero Technical Dependency
The system isn’t hacked—the user gives access voluntarily
✔️ Highly Personalized Attacks
Messages are customized based on the target
✔️ Almost Invisible
Difficult for traditional security tools to detect
✔️ High Success Rate
Because human behavior is often predictable
Why Social Engineering is More Dangerous Than Hacking
In traditional hacking, attackers must break into systems.
In social engineering, the system is already opened—by the user.
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

