FTK Imager is a widely used digital forensics acquisition tool that allows investigators to capture, preview, and verify digital evidence without altering the original data.
It is part of the
Forensic Toolkit (FTK) ecosystem and is trusted by:
- Law enforcement agencies
- Cyber forensic analysts
- Incident response teams
- Ethical hackers
- Digital investigation professionals
👉 Its main purpose is evidence acquisition (imaging), not analysis.
Core Capabilities
Disk Imaging (Forensic Copy)
- Create exact copies of:
- Hard drives
- USB drives
- Memory cards
- Supports formats like:
- E01 (EnCase)
- RAW (dd image)
👉 Ensures bit-by-bit copy of original evidence
Memory Capture (RAM Dump)
- Capture live system memory
- Useful for:
- Malware analysis
- Volatile data investigation
- Running processes detection
File Preview Without Modification
- View files directly from disk/image
- No risk of altering evidence
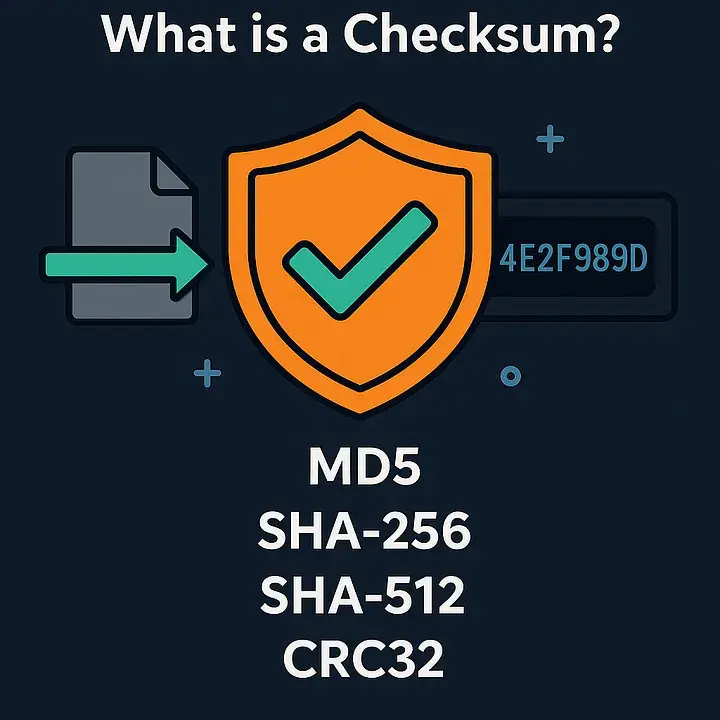
Hash Verification
- Generate MD5 / SHA hashes
- Ensure data integrity
- Validate evidence authenticity
Selective Data Export
- Extract specific files or folders
- Useful for targeted investigations
Advanced Features
✔️ Read-Only Access
Prevents accidental modification of evidence
✔️ Mount Image as Drive
Open forensic images like normal drives
✔️ Supports Multiple File Systems
✔️ Timeline & Metadata Preview
Quick look into file timestamps and attributes
Real-World Use Cases
- Cybercrime investigations
- Digital evidence acquisition
- Incident response (live systems)
- Malware analysis (RAM capture)
- Device forensic imaging
- Legal evidence preservation
Legal & Ethical Disclaimer
- Use only for authorized forensic investigations
- Always maintain chain of custody
- Unauthorized device imaging is illegal
- Follow legal compliance and privacy laws