ActivePerl + IP Locator is a bundled cybersecurity toolkit designed for automation, IP intelligence gathering, and OSINT-based investigations. This combination integrates a scripting engine with an IP tracking utility, allowing users to perform structured data analysis and location-based intelligence tasks.
The toolkit is commonly used by:
- Cybersecurity learners
- Ethical hackers
- OSINT researchers
- Digital investigators
- Network administrators
It is important to understand that this is not a direct hacking tool, but rather a supportive toolkit that helps in analyzing publicly available data and network-level information.
Component 1: ActivePerl (Scripting Engine)
ActivePerl is a professional Perl distribution developed by ActiveState, widely used for scripting, automation, and backend processing.
🔹 Key Capabilities:
- Run Perl-based cybersecurity and automation scripts
- Process large datasets (logs, IP lists, emails, etc.)
- Automate repetitive investigation tasks
- Integrate with APIs for real-time data fetching
- Cross-platform compatibility (Windows, Linux, macOS)
🔹 Practical Use:
- Parsing server logs for suspicious activity
- Automating bulk IP lookups
- Extracting structured data from raw sources
- Supporting other cybersecurity tools that rely on Perl
👉 In simple terms:
ActivePerl acts as the “execution engine” behind many cyber tools.
Component 2: IP Locator Tool
An IP Locator Tool is designed to retrieve geolocation and network-related data using an IP address as input.
🔹 Data You Can Extract:
- Country, State, City
- ISP (Internet Service Provider)
- Latitude & Longitude
- Time zone
- Basic network metadata
🔹 Common Use Cases:
- Fraud detection and investigation
- Email header tracing
- Website visitor analysis
- Suspicious login monitoring
- OSINT intelligence gathering
👉 Note: Accuracy depends on databases/APIs and is usually approximate, not exact.
How the Combo Toolkit Works
- ActivePerl runs custom or pre-built scripts
- Scripts connect to IP geolocation APIs or offline databases
- IP Locator processes and displays the results
- Output can be formatted into logs, reports, or dashboards
👉 Result:
A semi-automated cyber investigation environment that improves efficiency and speed.
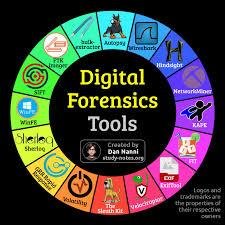
Advanced Features (Expanded Content)
✔️ Automation-Driven Analysis
Run bulk IP checks, automate workflows, and reduce manual effort.
✔️ OSINT Integration
Works well with Open Source Intelligence techniques and publicly available datasets.
✔️ Custom Script Support
Users can modify or create their own Perl scripts for specialized investigations.
✔️ Lightweight & Portable
Distributed in .rar format, easy to deploy on local systems without heavy requirements.
✔️ Beginner to Intermediate Friendly
Suitable for learners while still offering flexibility for advanced users.
✔️ API-Based Intelligence
Can integrate with third-party IP intelligence services for enhanced accuracy.
Real-World Applications
- Tracking suspicious login attempts
- Investigating phishing emails
- Monitoring web traffic sources
- Digital forensic pre-analysis
- Network anomaly detection
- Cybersecurity training environments
Legal & Ethical Disclaimer (Must Use on Website)
- This toolkit is intended strictly for educational and ethical cybersecurity purposes
- Users must comply with local laws and regulations
- Unauthorized tracking, surveillance, or misuse is illegal and punishable
- IP geolocation provides approximate data only and should not be treated as exact identification